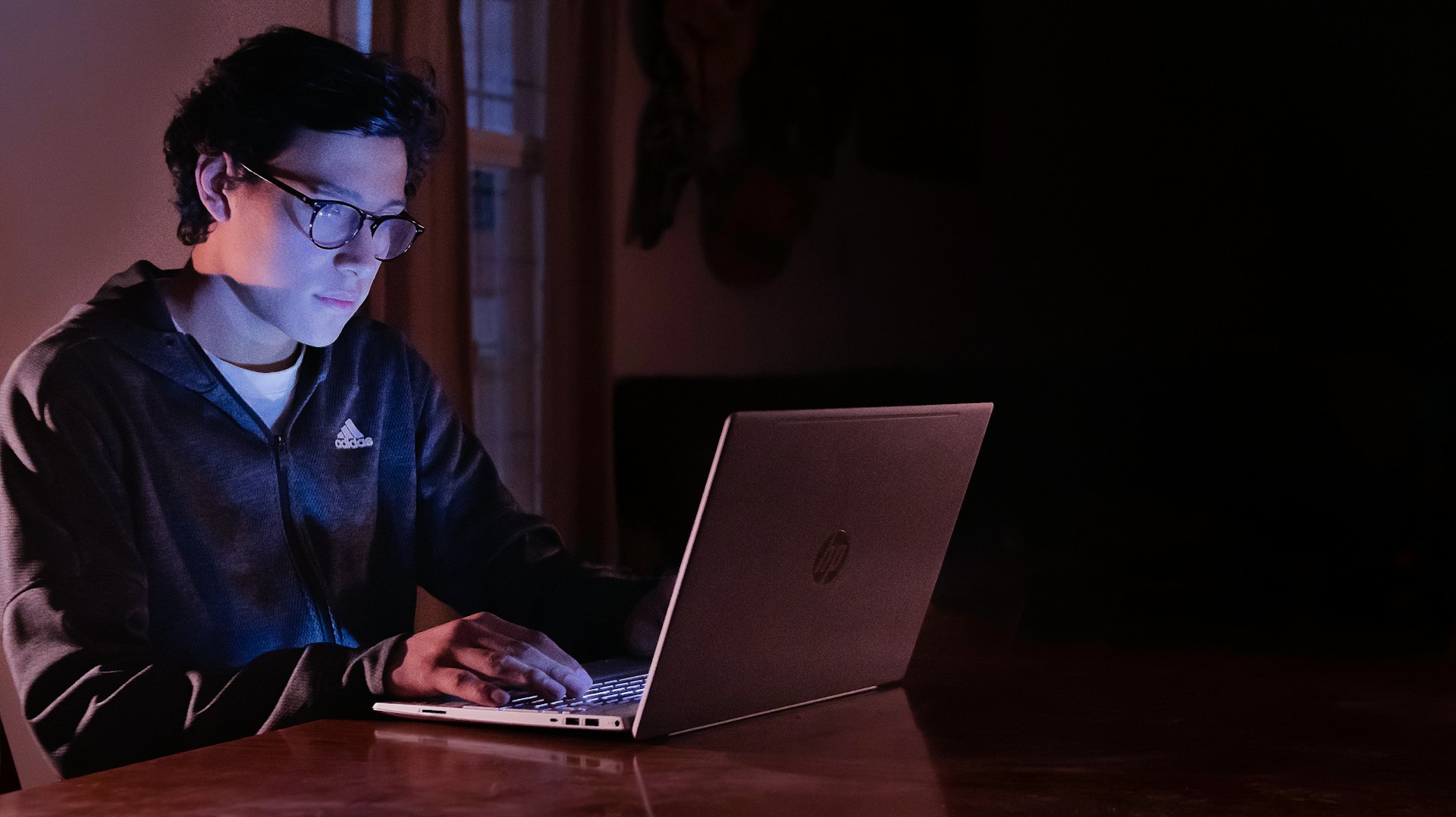
When the lights go out in the office, and inboxes finally go quiet, it’s easy to assume the digital world slows down, too. In reality, midnight is when many cyber threats come alive. Hackers know that fewer people are watching, response times are slower, and automated systems often carry the full weight of defense. Understanding what happens after hours can help businesses prepare for the risks that thrive in the dark.
Why Hackers Love the Late Shift
Late nights are prime time for attackers because human oversight drops dramatically. While security software runs, IT teams and employees are usually offline, so that suspicious activity may go unnoticed for hours. Businesses that rely on regional expertise, such as those working with Cybersecurity services in Columbus, often focus heavily on after-hours monitoring because attackers count on fatigue, silence, and delayed reactions to gain an edge.
Automated Attacks Never Sleep

One of the biggest misconceptions about cybercrime is that it requires constant human input. Many attacks are fully automated and designed to scan networks endlessly for weaknesses. After midnight, these bots continue testing login portals, probing outdated software, and attempting credential-stuffing attacks. The lack of real-time human intervention gives automated threats more room to maneuver and sometimes succeed before alarms are addressed.
Ransomware’s Favorite Window
Ransomware operators often schedule their attacks for the quietest hours of the night or early morning. The goal is simple: encrypt systems while no one is actively using them. By the time employees log in, the damage is already done, and panic sets in. Overnight encryption also increases the likelihood that network-connected backups are compromised before anyone can isolate the threat.
The Role of Insider Risk After Hours

Not all after-midnight threats come from outside. Insider risks, whether malicious or accidental, are more likely to occur during off-hours when supervision is minimal. A tired employee working late might bypass security steps, or a disgruntled insider could exploit the lack of oversight. These scenarios are more complex to detect at night, especially if logging and alert reviews are postponed until morning.
Monitoring, Alerts, and the Human Gap
Even with modern tools, alerts triggered at 2 a.m. may sit untouched for hours. This human gap is what attackers rely on most. Security systems can flag anomalies, but without a rapid response, threats can spread laterally through a network. Businesses that invest in 24/7 monitoring significantly reduce this risk by ensuring alerts lead to immediate action, not just morning reports.
Cyber threats don’t follow a nine-to-five schedule. After midnight, attackers become bolder, automated tools work overtime, and the absence of human eyes creates opportunity. Recognizing how digital threats behave when no one’s watching is the first step toward stronger protection. With the right combination of technology, monitoring, and awareness, businesses can sleep a little easier, knowing their defenses are just as alert at 3 a.m. as at noon.